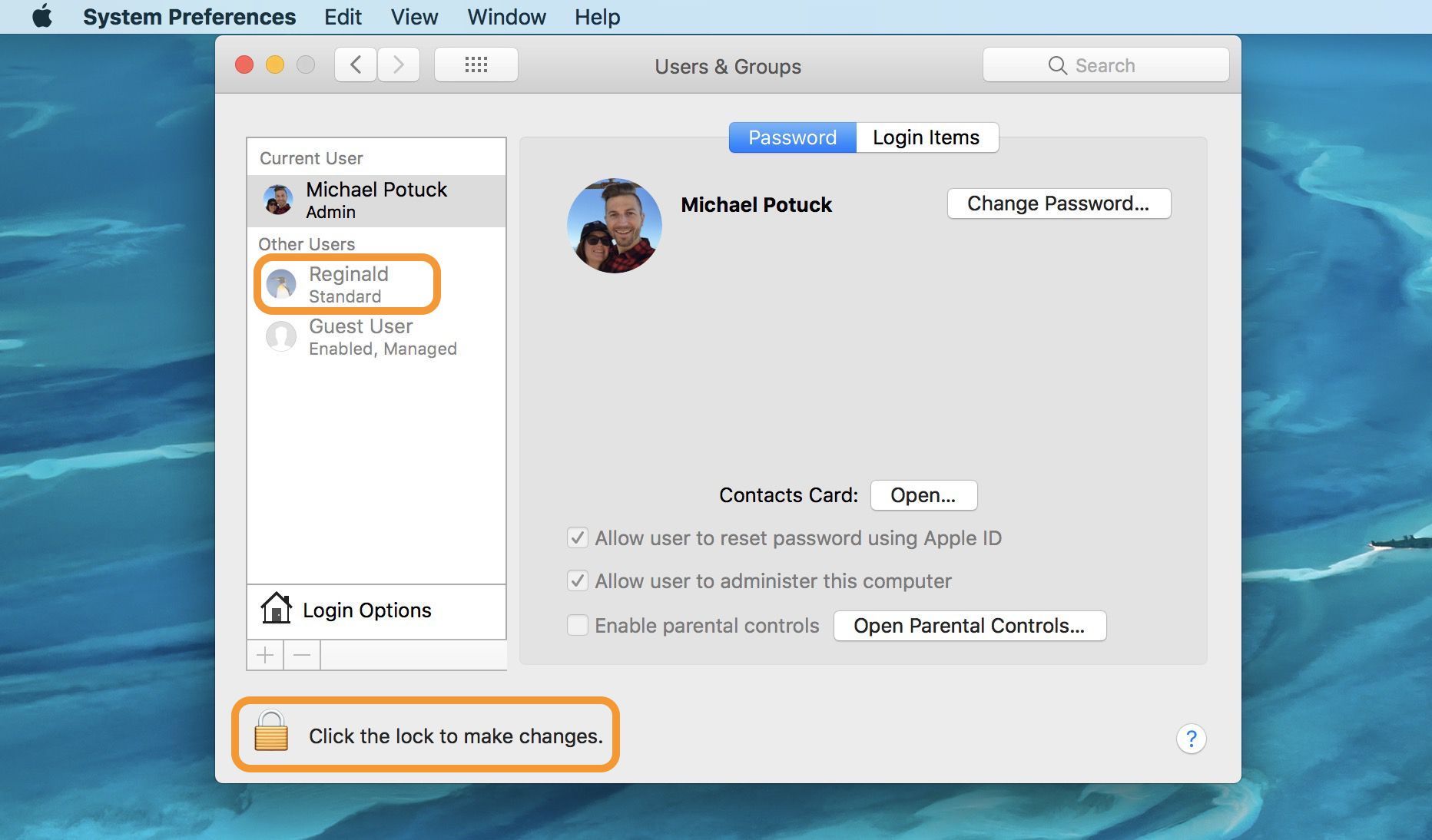
How to remove a mac user –
How to Remove a Mac User sets the stage for this comprehensive guide, offering readers a step-by-step approach to safely remove a local Mac user account without affecting system stability or user permissions.
Removing a local user account on a Mac computer can be a crucial task, especially when dealing with shared systems or obsolete accounts. In this article, we’ll delve into the benefits of user account removal, discuss various management methods, and provide a detailed guide on how to safely remove a local user account without disrupting system stability or user permissions.
Removing Administrator Rights to Enhance System Governance
Removing administrator rights from a Mac computer can have several implications for both user privileges and system management. On one hand, it can improve the security of the system by limiting the potential for malicious actions. On the other hand, it may also restrict certain users from performing necessary administrative tasks, which could impact their productivity and user experience.
Removing administrator rights can help to prevent unauthorized changes to the system, which can improve its overall security. However, it also means that users will need to obtain the assistance of an administrator in order to make certain changes or updates, which can lead to potential delays and complications.
Key Differences Between Administrator, Standard, and Guest User Accounts
Administrator, standard, and guest user accounts have distinct roles in system security and user experience. Understanding the differences between these types of user accounts is crucial for managing system governance effectively.
- Administrator User Account:
An administrator user account has full access to system resources and settings. This includes the ability to install software, modify system configurations, and make changes to user accounts. - Standard User Account:
A standard user account has limited access to system resources and settings. This includes the ability to perform everyday tasks such as browsing the web, creating documents, and running applications. - Guest User Account:
A guest user account has very limited access to system resources and settings. This includes the ability to use certain applications and access specific folders, but no ability to make changes or modifications.
Methods for Removing Administrator Rights
There are several methods for removing administrator rights from a Mac computer, each with its own set of advantages and disadvantages. Understanding these methods can help users make informed decisions about how to manage system governance.
- User Role Changes:
Changing the role of a user from administrator to standard or guest can limit their access to system resources and settings. This method is useful for preventing unauthorized changes and improving system security. - Permission Adjustments:
Adjusting permissions on specific files and folders can limit a user’s ability to make changes or modifications. This method is useful for protecting sensitive data and maintaining system security.
Key Considerations for Implementing System Governance
Implementing system governance effectively requires careful consideration of several key factors. These include the types of user accounts used, the access controls in place, and the permissions granted to users.
- User Account Types:
Using a combination of administrator, standard, and guest user accounts can help to balance system security with user productivity. - Access Controls:
Implementing access controls such as passwords, biometric authentication, and two-factor authentication can help to prevent unauthorized access and maintain system security. - Permission Adjustments:
Adjusting permissions on specific files and folders can help to protect sensitive data and maintain system security.
Benefits and Drawbacks of Removing Administrator Rights
Removing administrator rights from a Mac computer can have both benefits and drawbacks, depending on the specific context and use case. Understanding these benefits and drawbacks can help users make informed decisions about how to manage system governance effectively.
- Benefits:
Removing administrator rights can help to improve system security by limiting the potential for malicious actions. - Drawbacks:
Removing administrator rights can also restrict certain users from performing necessary administrative tasks, which could impact their productivity and user experience. - Disable access to sensitive directories and files
- Update firewall rules to block the removed user’s IP address
- Remove the user’s SSH keys and passwords
- Verify and update password policies for remaining user accounts
- Review file ownership and group memberships
- Update file permissions to restrict access to sensitive files
- Verify that system-critical files and directories have appropriate permissions
- Remove access to files and directories created by the removed user
- Review user roles and memberships
- Update system group memberships to reflect the removed user
- Verify that critical system functions have appropriate permissions and access controls
- Remove access to system-critical functions for the removed user
- Monitor system logs for errors and warnings related to the removed user
- Verify that system-critical functions are accessible and functioning correctly
- Test system access and permissions to ensure that remaining user accounts have proper access
- Run system integrity checks to detect potential issues and vulnerabilities
- Remove the removed user’s account from system group memberships
- Update file permissions to restrict access to files and directories created by the removed user
- Remove SSH keys and passwords for the removed user
- Update password policies for remaining user accounts
- System crashes: These can occur when there are issues with system resources, drivers, or software.
- Permission errors: These can occur when the system cannot access certain files or folders due to missing permissions or corrupted user accounts.
- File corruption: This can occur when the system cannot access certain files or folders due to issues with disk permissions or corrupted user accounts.
- Inadequate preparation for user account removal
- Insufficient troubleshooting of system issues before removal
- Corrupted system files or drivers
- Missing or corrupted user account information
- Insufficient disk space or disk errors
Maintaining System Integrity Post-User Removal

Maintaining the integrity of a system after removing a user account is crucial to ensure the continuity of operations and prevent potential security breaches. Removing a user account does not automatically update the system’s security settings, file permissions, or user roles, making it essential to verify and update these components.
Security Settings Update Checklist, How to remove a mac user
When removing a user account, it is critical to review and update the system’s security settings to prevent unauthorized access. Here’s a checklist of essential security settings to verify and update:
File Permissions Update Checklist
Updating file permissions is another critical step in maintaining system integrity. Here’s a checklist of essential file permissions to verify and update:
System Roles and Permissions Update Checklist
Updating system roles and permissions ensures that only authorized users have access to critical system functions. Here’s a checklist of essential roles and permissions to verify and update:
Verifying System Stability and Detecting Potential Post-Removal Issues
After updating security settings, file permissions, and system roles, it is essential to verify system stability and detect potential post-removal issues. Here’s a step-by-step guide to follow:
Updating System Permissions and User Roles
Updating system permissions and user roles ensures that the removed user’s account no longer has access to system-critical functions. Here’s a step-by-step guide to follow:
Troubleshooting Common Issues Post-User Removal
When you remove a user account from a Mac, you might encounter some issues that can disrupt the smooth functioning of your system. These issues can range from system crashes to permission errors and file corruption. Troubleshooting these problems is essential to ensure that your system continues to operate efficiently after the user account has been removed.
In this section, we will investigate common issues that may arise after removing a user account, identify potential causes of these issues, and provide troubleshooting steps for resolving them.
Common Issues and Their Causes
Some common issues that may arise after removing a user account include:
These issues can arise from various causes, such as:
Troubleshooting Steps for Common Issues
To troubleshoot these common issues, follow these steps:
1. Restart your Mac: Sometimes, a simple reboot can resolve system crashes and other issues related to system resources.
2. Run a System Report: Run the System Report utility to identify potential issues with system files, drivers, and software. This can help you pinpoint the cause of the issue and take corrective action.
3. Check Disk Permissions: Check the disk permissions for the affected user account or files to ensure that they are correctly set up.
4. Run a Disk Utility Check: Run a disk utility check to identify and repair any disk errors that may be causing the issue.
5. Restore from a Time Machine Backup: If all else fails, consider restoring from a Time Machine backup to roll back to a point before the user account was removed.
Case Study: Resolving Post-User Removal Issues
One real-life example of a system that experienced post-user removal issues is as follows:
Case Study: System Crashes after User Account Removal
A user had a Mac system that was used by multiple users. After removing a user account, the system crashed repeatedly, and the user encountered permission errors and file corruption.
To resolve the issue, the system administrator:
* Restarted the Mac several times to resolve system resource issues.
* Ran a System Report to identify corrupted system files and drivers.
* Checked disk permissions for the affected user account and files.
* Ran a Disk Utility Check to repair disk errors.
* Restored from a Time Machine Backup to roll back to a point before the user account was removed.
By following these troubleshooting steps, the system administrator was able to resolve the post-user removal issues and restore the system to its optimal state.
Conclusive Thoughts: How To Remove A Mac User
![How to Delete a User on Mac in 2 Easy Steps [2024] How to Delete a User on Mac in 2 Easy Steps [2024]](https://appuals.com/wp-content/uploads/2024/03/Users-highlighted-on-macOS-Sonoma-Lock-Screen.jpg)
In conclusion, removing a Mac user can be a daunting task, but with this guide, you’ll be empowered to tackle it with confidence. Remember to always backup your data, update system permissions, and verify system stability post-removal.
Questions Often Asked
Q: How do I recover deleted files after removing a user account?
A: You can try recovery software like Time Machine or Disk Drill to recover deleted files.
Q: Can I remove a user account without affecting system stability?
A: Yes, follow our step-by-step guide to safely remove a local user account.
Q: What happens when I remove a user from Apple ID and parental controls?
A: Removal of user account from Apple ID will revoke device permissions and disable cloud services. Parental controls removal will adjust content restrictions and access permissions.